Automated Targeting System (ATS)
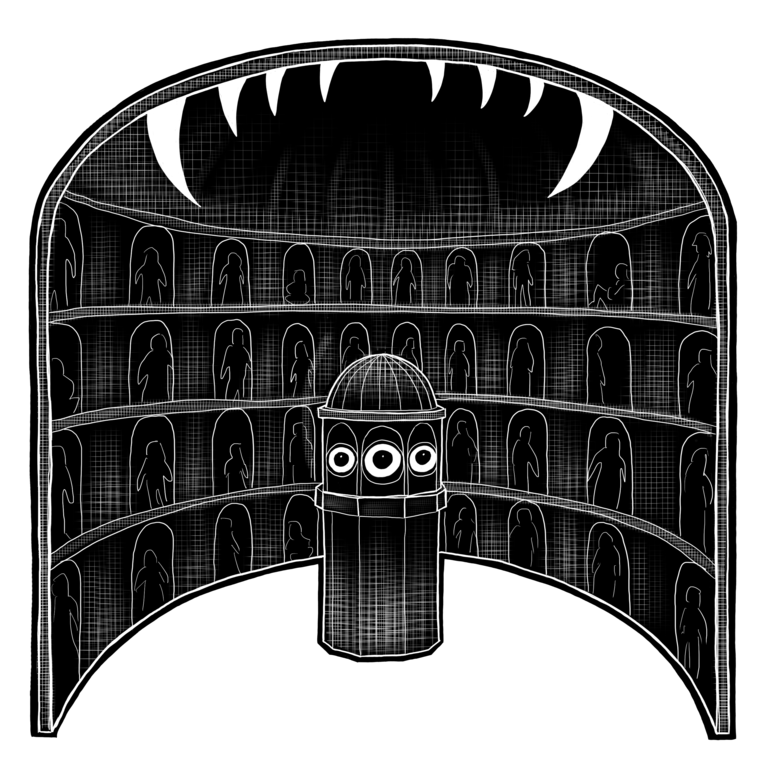
The Automated Targeting System (ATS), is CBP’s main computer system that defines and predicts “risk,” and is one of the most important connective databases for current migrant data criminalization processes. CBP uses ATS to track and target as “risky” certain travelers with US immigrant and nonimmigrant visas, and import trade goods.Footnote 1 ATS relies on AI, black-box algorithms, based on criteria and rules developed by CBP, to match against against “lookouts” and data-scrape personal information from various linked databases to identify “patterns of suspicious activity” and predict potential terrorists, transnational criminals, people who may be inadmissible to the United States under US immigration law, and “persons who pose a higher risk of violating U.S. law” before they arrive in the United States.Footnote 2 Footnote 3
USCIS applicants for “benefits” like immigrant and nonimmigrant visas, or refugee status, are checked against ATS.Footnote 4 The details of their screenings are included in the database for future checks. Through “continuous vetting,” individuals connected to a USCIS immigration application benefit request will be subject to security checks upon receipt by USCIS and CBP, and ATS will stop recurrent vetting only when it receives a message from USCIS based on administrative closure from an immigration judge’s calendar or from the Board of Immigration Appeal docket, certificate of citizenship issue, denial, failure to pay, or withdrawn adjudication activities.
USCIS uses the information provided by ATS and other CBP databases to identify individuals “who may have a connection to potential identity or benefit fraud, national security or public safety concerns, and criminal activity.” In addition to form submission information, USCIS sends to CBP biographic, biometric identifiers, and encounter information from IDENT. ATS is able to retrieve these data elements through its existing IDENT interface.
The ATS system decides who will be added to a category of people who will be subject to increased security checks. In order to “train” its risk assessment, ATS uses data obtained from other governmental information systems including: electronically filed bills, entries, and entry summaries for cargo imports; manifests for arriving and departing passengers and crew; airline reservation data; nonimmigrant entry records; CBP incident logs; suspect and violator indices; state Department of Motor Vehicle Records, and seizure records. ATS flags all the people who categorically fit CBP’s targeting rules, and these individuals are then reviewed by CBP officers.
Continuous vetting occurs in real-time, as ATS alerts CBP, for instance, if a traveler’s ID check at a foreign airport brings up biographical or biometric matches to any records in criminalizing databases — including those that track immigration violations, the FBI’s Terrorist Screening Database (TSDB) and outstanding wants and warrants.Footnote 5 CBP can then issue a “no board” recommendation to prevent someone’s travel to the US, or recommend the DOS revoke a visa.
Like other data criminalization tools, ATS draws heavily from NCIC data — but it also surveils people who have never had an encounter with police.Footnote 6 A speaker at a 2004 Customs Budget Authorizations hearingFootnote 7 testified that ATS data scrapes airline passenger information to look for “anomalies and red flags.” Since “red flags” are determined based on rules for ATS that are created by CBP; these rules allow CBP to expand the list of what is considered suspicious activity to encompass any number of legal behaviors.Footnote 8 People who are deemed “high risk” by ATS are sent to secondary screening at US border and airport checkpoints. Those encounters lead to the generation of yet more data criminalization records, in the form of risk assessments retained by ATS, which are fed into the targeting algorithm that could alert a TSA or CBP agent the next time the person’s passport is scanned.
The evolution of ATS’ targeting rules reveals the trajectory of terrorism and surveillance rhetoric. Mass surveillance that began as exceptional (the post-9/11 period) and provisional (pilot programs at 15 airports) is now routine — and probable cause for law enforcement intervention (which can end in arrest and deportation) includes not only subjective suspicion but fully abstracted prediction mathematics. Today, ATS is utilized by CBP to predict who might violate US immigration (not just anti-terrorism) laws: ATS data is used to generate an “Overstay Hotlist,” which is a list of “overstay leads” derived from information obtained through travel records.Footnote 9
ATS has built its dataset over decades, well before 9/11. ATS-Passenger (ATS-P), a legacy subsystem of ATS, has been used to screen international passengers on planes, trains and ships since the 1990s — although data collection for ATS overall was expanded and automated since 2002.Footnote 10 ATS-P is now being upgraded to UPAX, which more seamlessly integrates databases by showing records from multiple systems and incorporating information from third-party databases and the Internet.Footnote 11 ATS creates a “gallery” out of archived photographs from CBP’s ATS-UPAX database that draw from previous exits and entries, US passports and visas, from DHS apprehensions, enforcement actions, or other immigration-related records. This gallery is used by CBP’s facial recognition matching technology, the Traveler Verification Service (TVS), to match live images of the traveler on the jetway (often taken secretly) with archived photos in order to “confirm identity.”
ATS makes use of warrantless searches of electronic devices, such as cell phones and laptops, which are permitted at US borders and part of the process that accumulates material and trains algorithms for data criminalization.Footnote 12 An ATS Privacy Impact Assessment from May 2020 explains: “Searches can be vital to risk assessments that otherwise may be predicated on limited or no advance information about a given traveler or item. Digital information extracted from electronic devices and saved in ATS may relate both to the owner of the device, as well as his or her contacts.”Footnote 11 DHS can make use of extracted or copied digital data from electronic devices in multiple ways. The ATS-TF (Targeting Framework) module allows users to perform research and analysis by integrating data from multiple sources, including from electronic devices, and to show possible relationships between entities and data elements.
CBP combines visa overstay “lead” predictions calculated by its Arrival and Departure System (ADIS) and Student and Exchange Visitor Information System (SEVIS) database, which track noncitizens who enter the United States as students and exchange visitors, and forwards this list to ATS. ICE agents and other law enforcement can also add people directly into the ATS system.Footnote 13
Every person who leaves or enters through a US border is subject to ATS’ risk assessment, and while different linked databases claim to delete data at different times, much ATS data is kept for at least 15 years, some for much longer.
Mass surveillance practices in travel have normalized data criminalization entirely, effectively making de facto criminalization the norm, rather than an exception that requires some amount of justification from the accuser. A 2020 DHS report on data mining explained: “When evaluating risk, ATS is designed to apply the same methodology to all individuals to preclude any possibility of disparate treatment of individuals or groups.”Footnote 14 Literally, what that means is that everyone begins their journey evaluated as a suspect.
ATS can access, query or ingest data in real-time from the following systems (in addition to others):
- DHS collects some data directly from commercial carriers, or from the computerized reservation system to which airlines outsource hosting of reservations. This includes:
- Passenger Name Records (PNRs) for international flights
- Advance Passenger Information (API) for international travel by air, sea, or land
- Secure Flight Passenger Data (SFPD) for domestic flights, via the TSA
- Advance Passenger Information System (APIS)
- Electronic System for Travel Authorization (ESTA)
- SEVIS: ICE’s Student Exchange and Visitor Information System
- EID
- TECS/ ICM
- Nlets
- NCIC
- IDENT/ HART
- USCIS’s Person Centric Query System, PCQS (more below)
- CCD
- commercial data aggregators